AI-Powered Data Security & DSPM:
Visibility, Control, and Remediation at Scale
Built for security teams who need more than legacy DLP. BigID combines AI-driven data security posture management (DSPM), automated classification, and zero trust access intelligence — across multi-cloud and hybrid environments — to reduce your attack surface before threats materialize.
With BigID Next, your security program gets:
- Integrated DSPM for continuous data risk visibility across cloud, SaaS, and on-prem
- AI-driven classification to automatically find sensitive, regulated, and high-risk data — 95% faster than legacy tools
- Automated remediation workflows so the right teams take the right actions on the right data
- Zero trust access intelligence to enforce least-privilege and eliminate over-exposure
-
AI security controls to govern data entering and exiting LLMs and generative AI pipelines





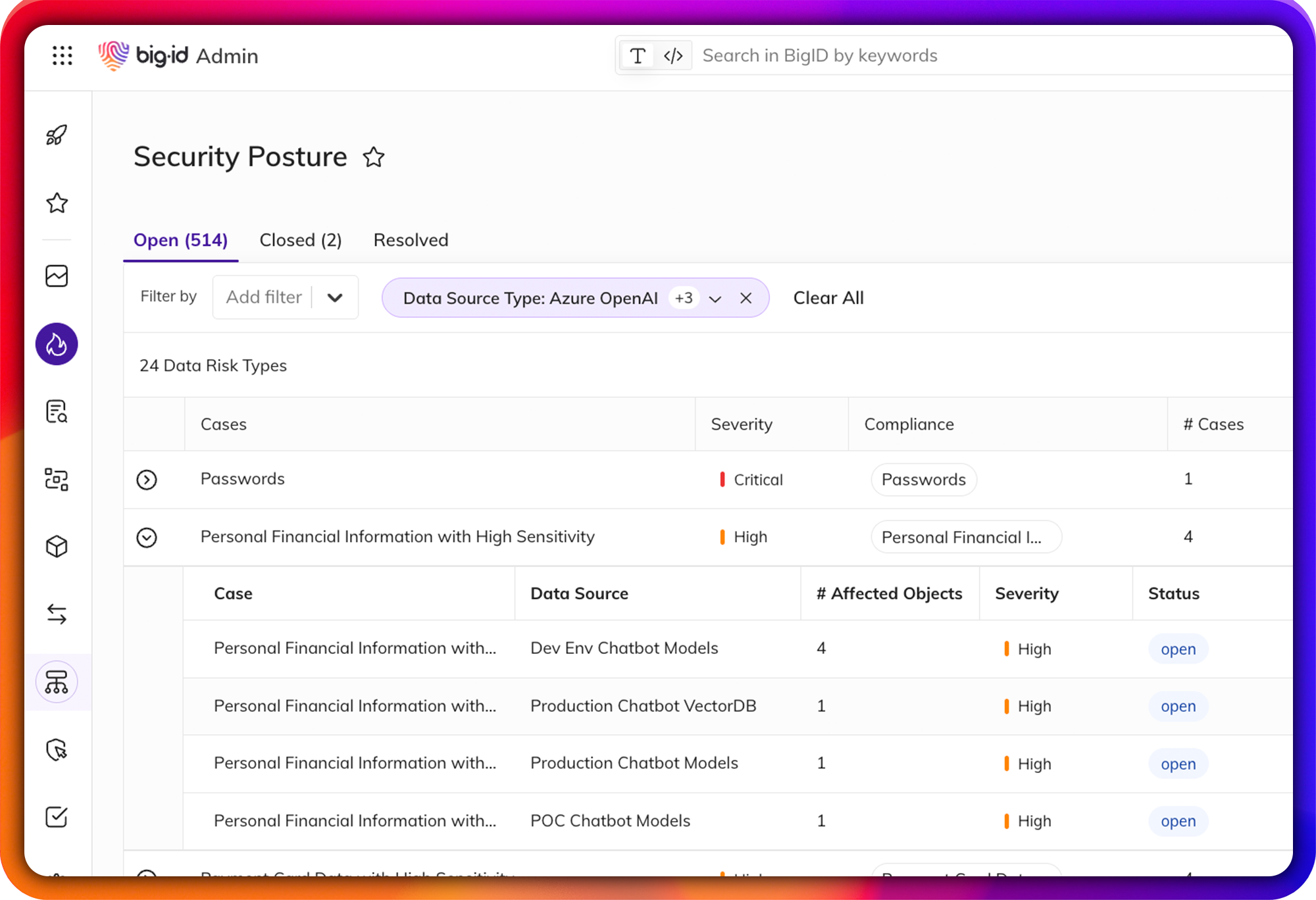
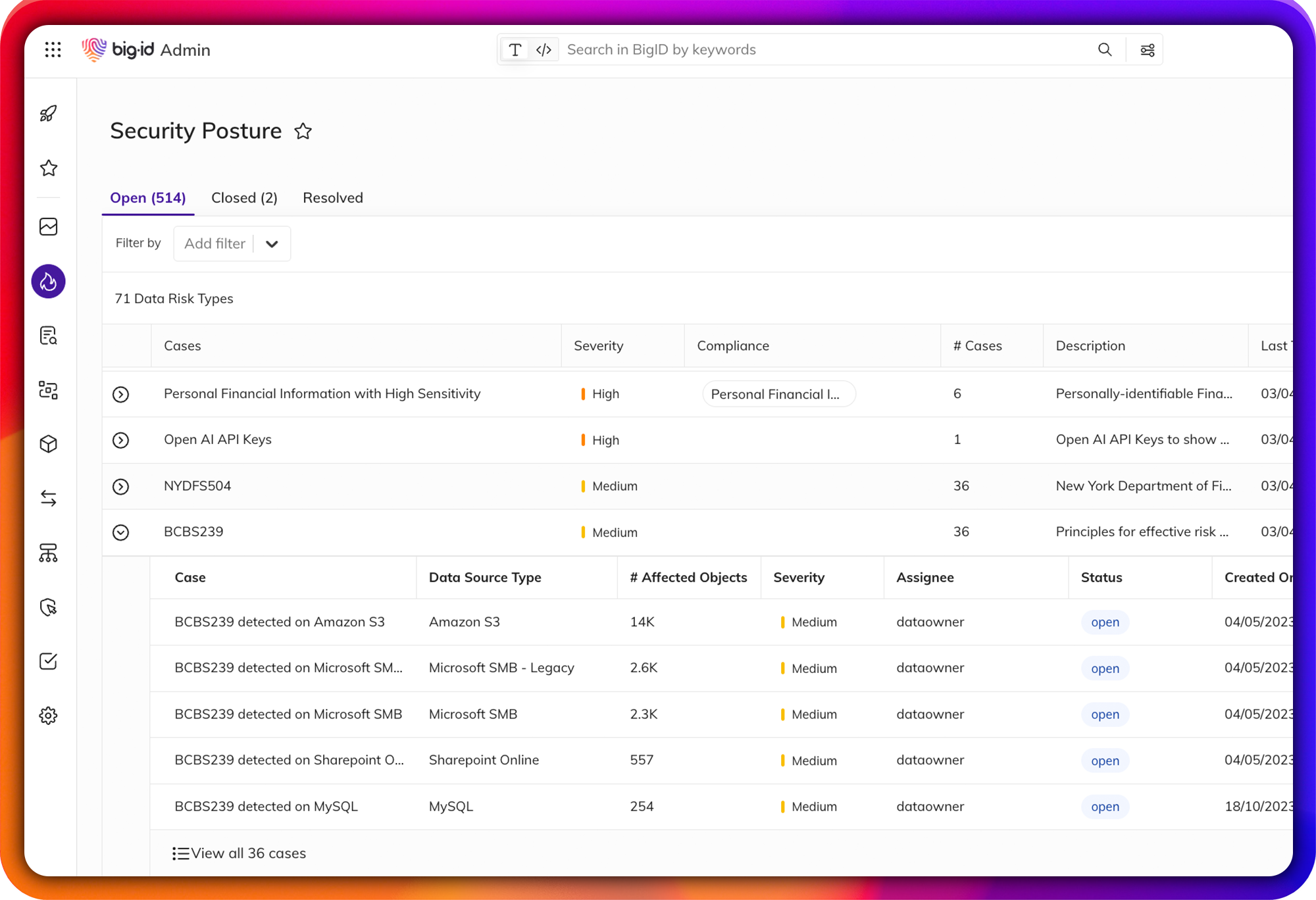
Jumpstart Data Security Posture Management (DSPM)
Proactive, data-centric DSPM for the multi-cloud era.
Accelerate your DSPM program with a data-first approach. BigID automatically maps, monitors, and remediates data risk across the multi-cloud — powered by ML-driven in-depth data discovery and automation. Get continuous visibility into your data security posture without manual inventories or point-in-time snapshots.
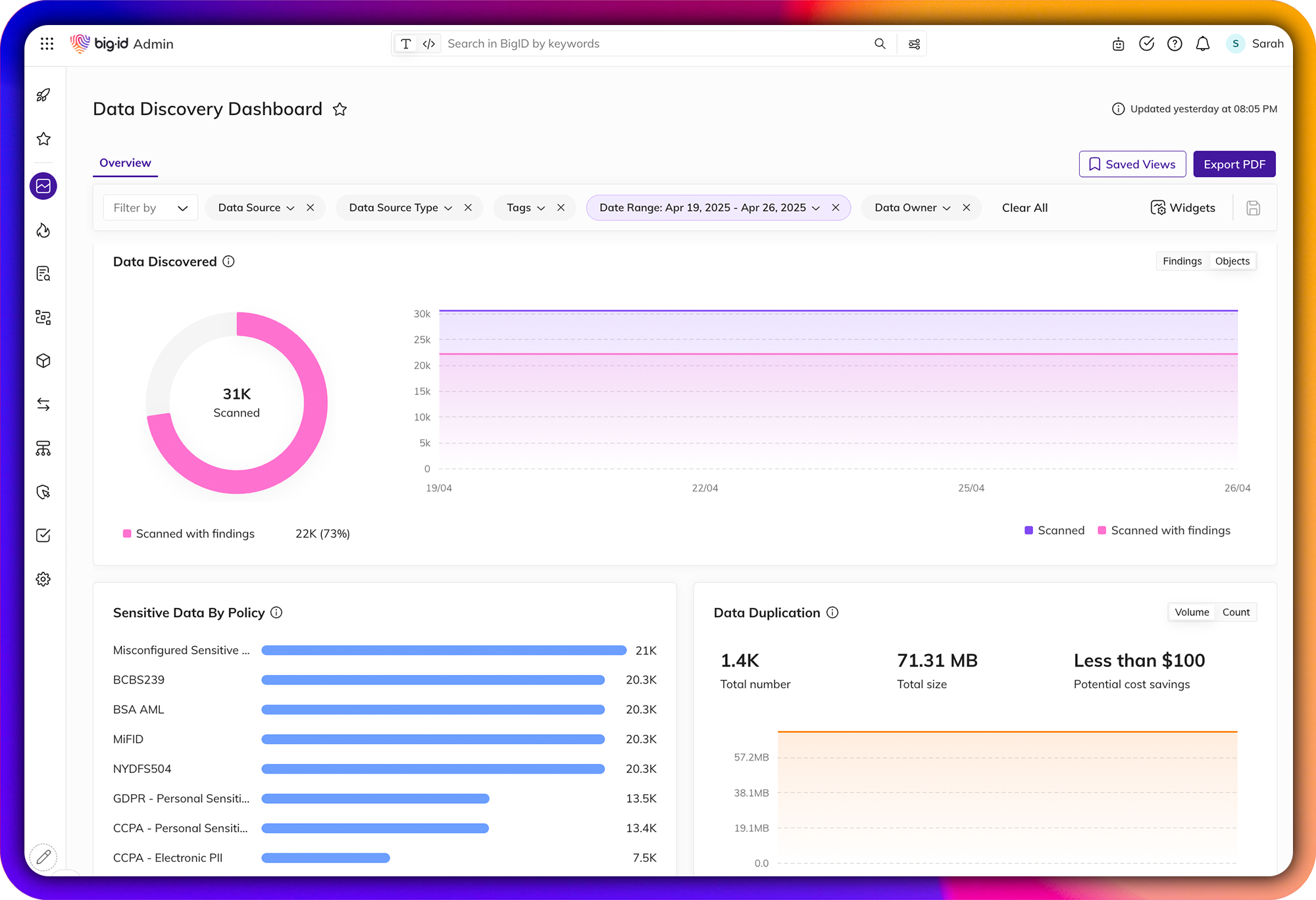
Shine a Light on Dark Data
Automatically discover and inventory your most sensitive and critical data — wherever it lives.
Get unmatched data discovery and classification to find the data that matters most: regulated PII, financial records, IP, credentials, secrets, and more. ML-driven classification delivers faster, more accurate results across structured and unstructured data — from on-prem to cloud to SaaS.
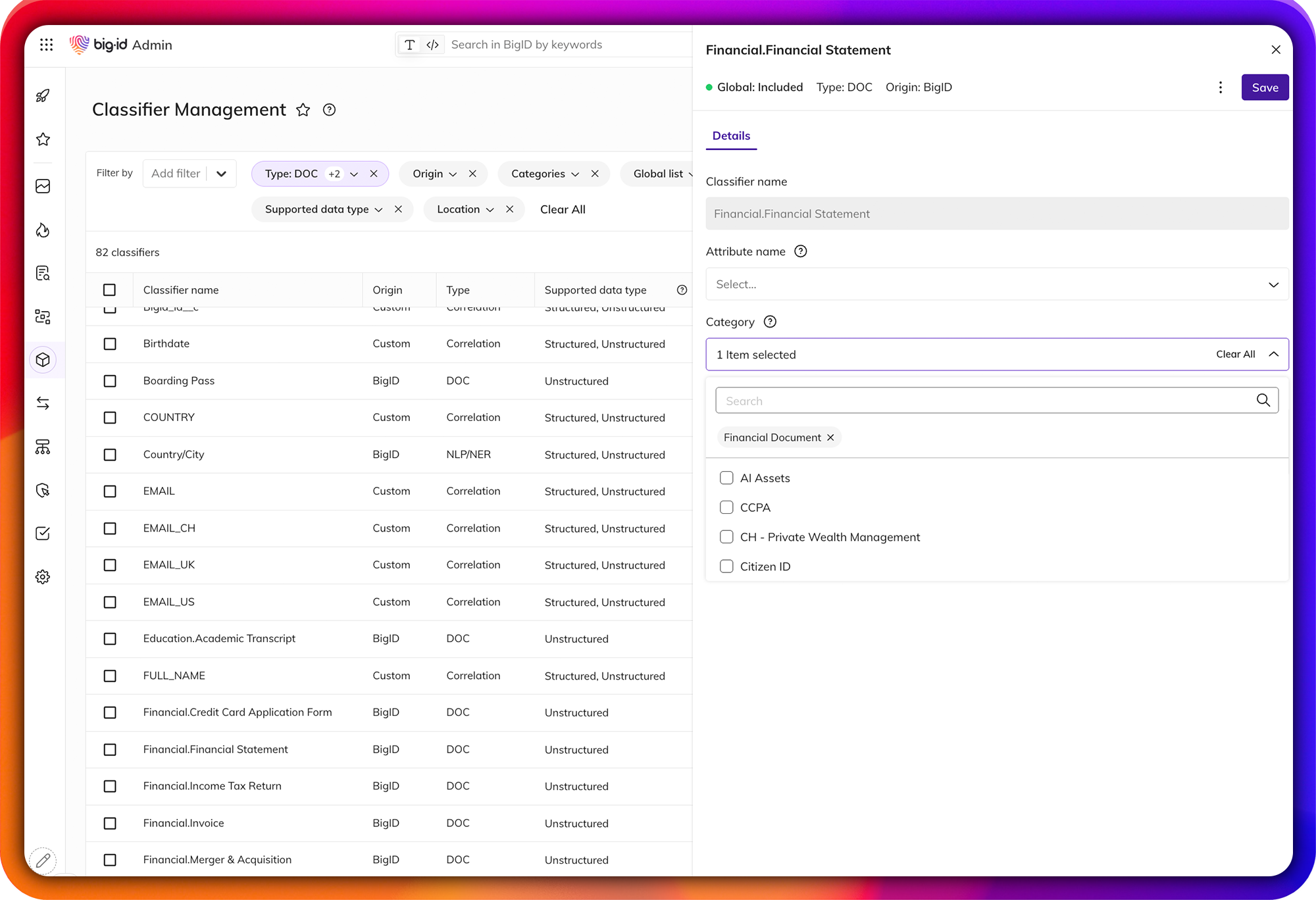
Advanced Sensitivity Classification for Security Teams
Achieve unparalleled accuracy and scalability in data classification.
Go beyond static RegEx and pattern-matching with advanced, trainable ML and NLP-based classifiers. Build custom classifiers tuned to your environment. Test and fine-tune before deployment to reduce false positives. Apply a single unified classification ruleset across your entire data landscape — with consistent labeling that feeds downstream security workflows.
Data-Centric AI Security & Risk Governance
Identify and govern sensitive data in AI models — before it becomes a breach.
BigID helps security teams proactively identify sensitive, toxic, and high-risk data fueling AI models — reducing exposure, ensuring compliance, and minimizing AI risk. Whether it's PII in LLM training data, IP in generative AI pipelines, or shadow AI across business units, BigID provides the visibility and control security teams need across multi-cloud and on-prem environments.Streamline Data Protection Workflows & Remediate Risk
Remediate high-risk, sensitive, and critical data — everywhere — from one place.
A single pane of glass for all data protection actions: annotate, delete, quarantine, archive, mask, encrypt, and anonymize sensitive data. Assign findings and tasks to the right data owners, maintain a full audit trail of all data protection activity, and enforce remediation priorities by policy. Report on actions taken on sensitive data for compliance purposes..png?width=2000&height=1368&name=ai-remediation%20(1).png)
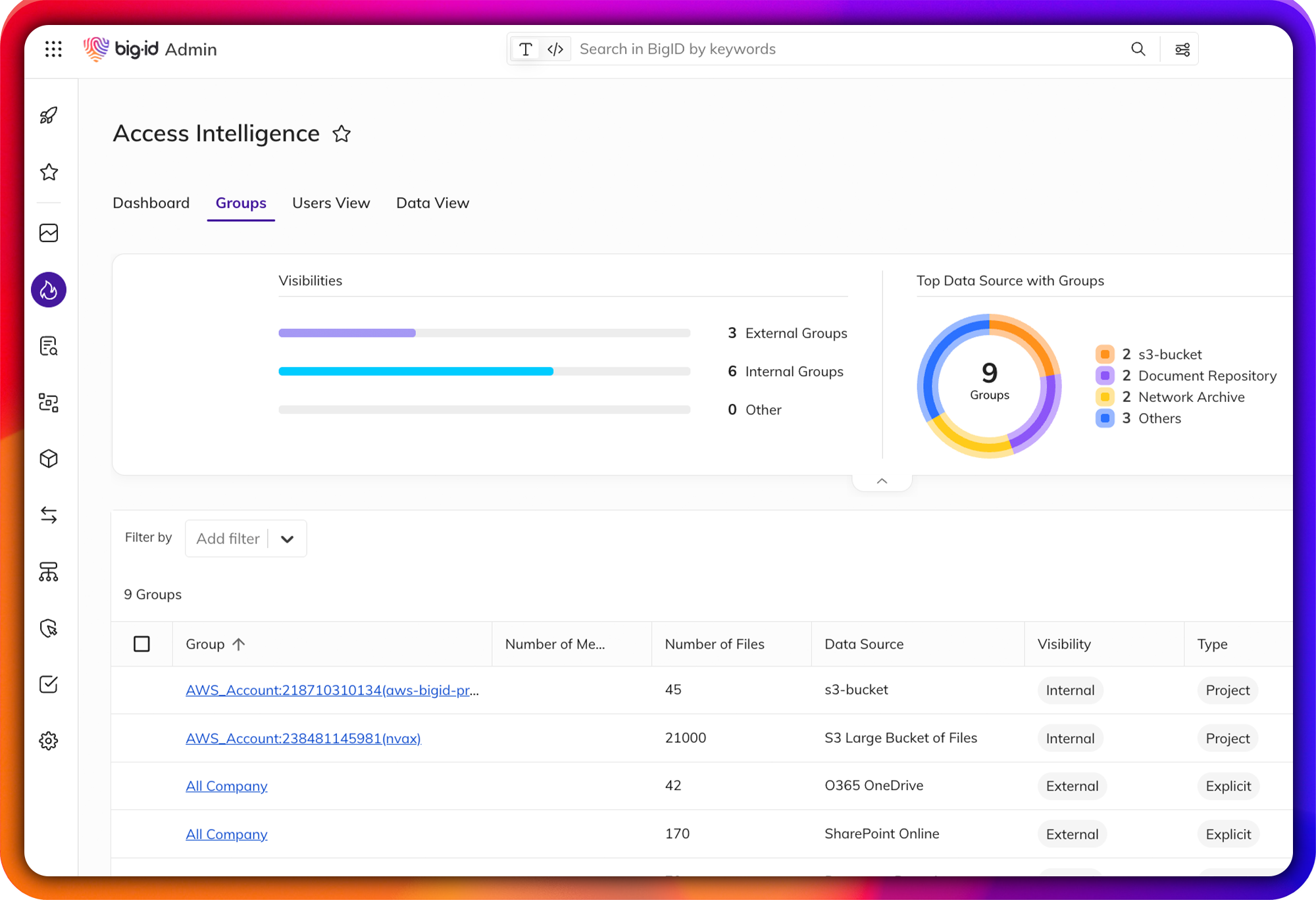
Enable Zero Trust for Data
Identify and remediate high-risk data access issues across your data landscape.
Find over-permissioned and over-exposed data across your entire environment. Mitigate unauthorized use, reduce the risk of data leaks or breaches, and move toward a least-privilege permissions model that supports your zero trust architecture.
Integrates with Your Security Stack
BigID is built as an open, API-first platform that integrates and orchestrates workflows with your existing enterprise infrastructure. Native connectors span 500+ data sources across cloud, on-prem, SaaS, PaaS, IaaS, dev tools, big data platforms, and email.
Technology partnerships include: Snowflake, Microsoft, AWS, Google Cloud, Salesforce, ServiceNow, Splunk, Collibra, Alation, SAP, Confluence, and more.
Want to see more before your demo?
Case Study: University of Maryland
The University of Maryland used BigID to uncover and remediate over $5 million in data risk exposure across 2.5 petabytes of cloud storage. Deep discovery and classification across Google Drive, Microsoft 365, and Box identified thousands of exposed PII records — improving compliance posture and reducing organizational risk.
FAQ:
What data sources does BigID cover?
BigID connects to 500+ data sources natively — including SaaS platforms, PaaS and IaaS environments, dev tools, applications, big data and NoSQL systems, email platforms, and on-premises data centers — at petabyte scale. This includes structured, semi-structured, and unstructured data across cloud, hybrid, and air-gapped environments.
Does BigID cover unstructured and semi-structured data?
Yes. BigID provides comprehensive coverage across all data types — structured, semi-structured, and unstructured. This enables discovery of dark data and sensitive records across documents, emails, images, code repositories, and more. BigID combines RegEx with advanced ML and AI to scan your data 95% faster than legacy tools.
Will BigID integrate with my existing tech stack?
BigID is an open, API-first platform designed to integrate with your enterprise infrastructure. Existing partnerships span Collibra, Alation, SAP, Salesforce, ServiceNow, Confluence, Splunk, Snowflake, Microsoft, Google Cloud, AWS, and hundreds more. Extensive APIs, documentation, and code samples are available for custom integrations.
What security use cases can BigID solve?
BigID addresses a broad range of data security use cases: improving data security posture (DSPM), enabling zero trust, managing insider risk, minimizing attack surfaces, accelerating cloud migration, validating M&A data risk, staying compliant with global regulations, governing data in AI pipelines, automating end-to-end data lifecycle management, and revolutionizing DLP with machine learning.
Shine a Light on Dark Data
Automatically find and inventory your most sensitive, critical, and high priority data - wherever it lives.
Get unmatched data discovery and classification to find the data that matters most to you: whether it's critical, regulated, personal, secrets, passwords, IP, financial, or more. Get more accurate results every time with ML-driven data classification - across your entire data landscape (from on-prem to cloud to everywhere in between).