Comply With DORA & Build Resilience Against Cyber Threats in Your Organization
Enforcement for the Digital Operational Resilience Act (DORA) is in effect. Are you compliant?
DORA establishes a framework to safeguard EU-based financial institutions and systems from cyber attacks and data risks. Achieve compliance and protect your data with BigID through automating data governance, improving ICT and security risk management, streamlining incident response and reporting, and testing resilience.
Talk to one of our data-centric DORA specialists 👇 and check out what we put together for you below.
-1.webp)
Recognized as the industry-leading data security, compliance, and AI governance solution




Navigating the DORA Framework
Achieve compliance with the new regulation and improve organizational resilience against cyber threats
The EU created DORA to establish a comprehensive framework to ensure financial entities can withstand, respond to, and recover from Information and Communication Technology (ICT)-related disruptions. Achieving compliance requires a proactive approach to cybersecurity, risk management, and operational resilience.
BigID is uniquely positioned to enable organizations to comply with DORA. With BigID, organizations can find, classify, and map all of their data for full visibility, automate data governance and lifecycle, assess and mitigate risk, and streamline effective incident response and reporting.

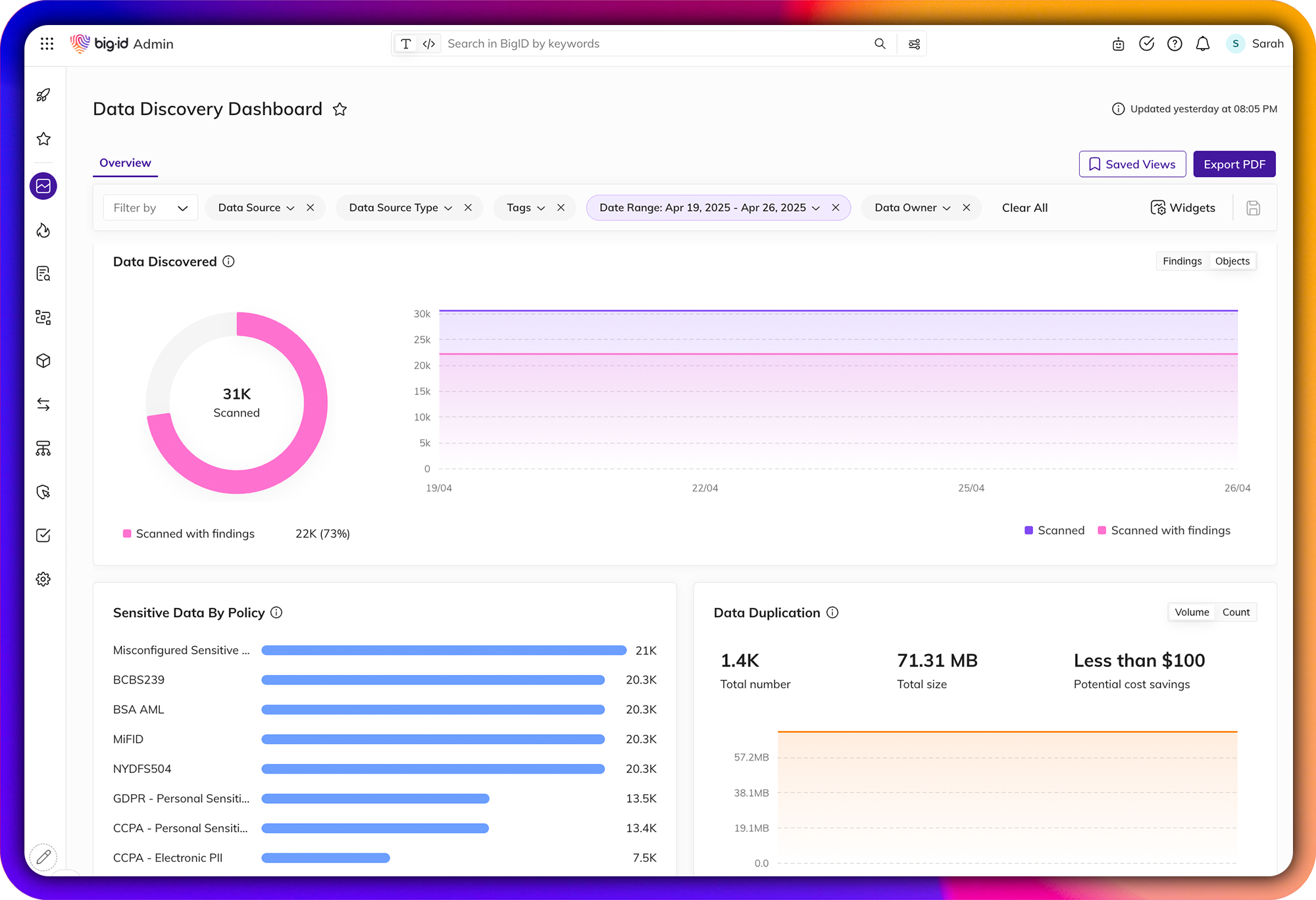
Shine a Light on Dark Data
Automatically find and inventory your most sensitive, critical, and high-priority data - wherever it lives.
Get unmatched data discovery and classification to find and protect the data that matters most to you: whether it's critical, regulated, personal, secrets, passwords, IP, financial, or more across structured and unstructured data. Get more accurate results every time with ML-driven data classification - across your entire data landscape (from on-prem to cloud to everywhere in between).
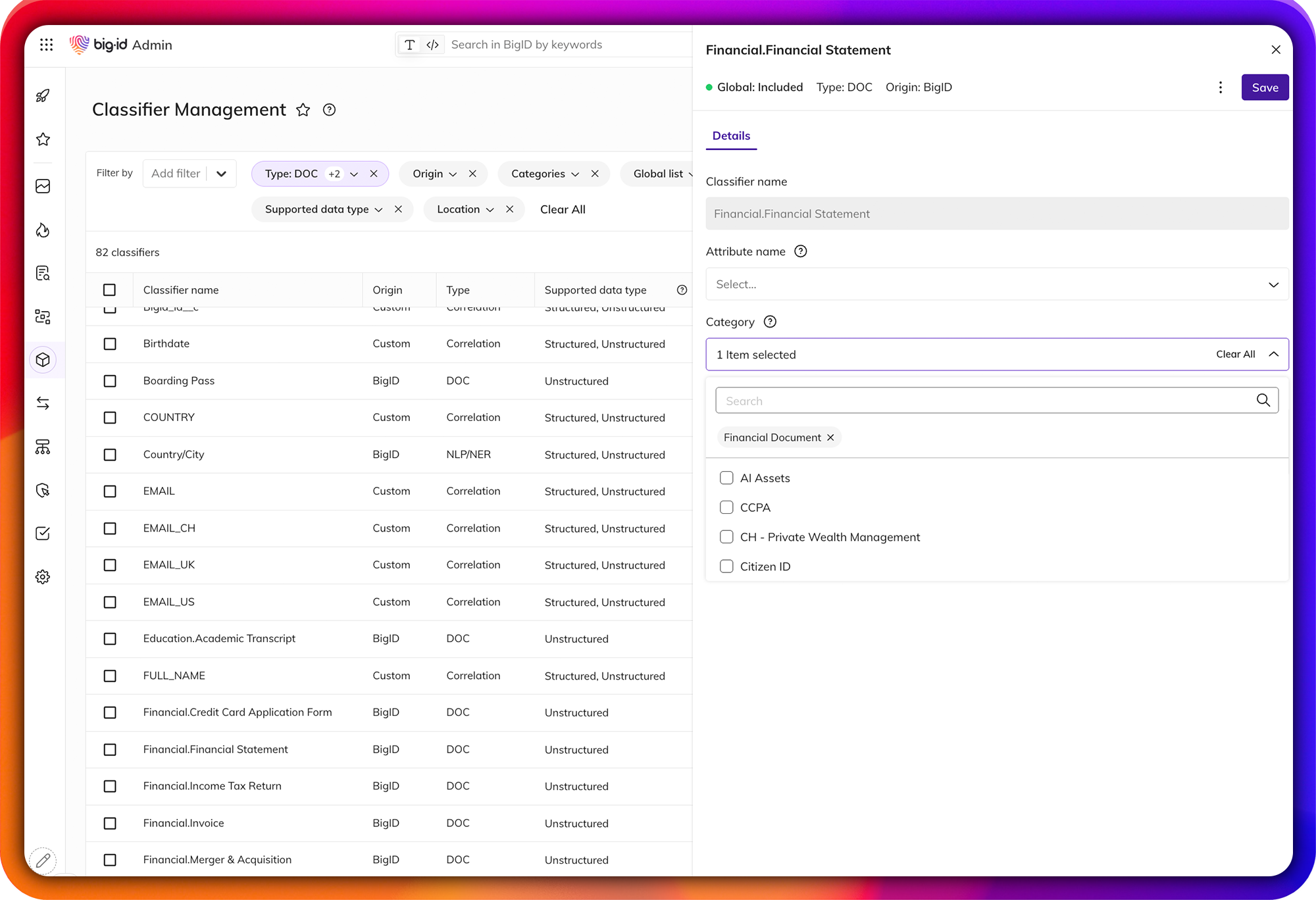
Advanced Data Classification
Achieve unparalleled accuracy and scalability in data classification for DORA compliance.
Go beyond traditional pattern-matching and regular expression (RegEx) with advanced, trainable ML and NLP-based classification. Create custom classifiers that can be tailored specifically to your unique data environment. Test and fine-tune them before deployment to enhance accuracy and mitigate the number of false positives. Label and tag all of your data using a single unified classification ruleset.
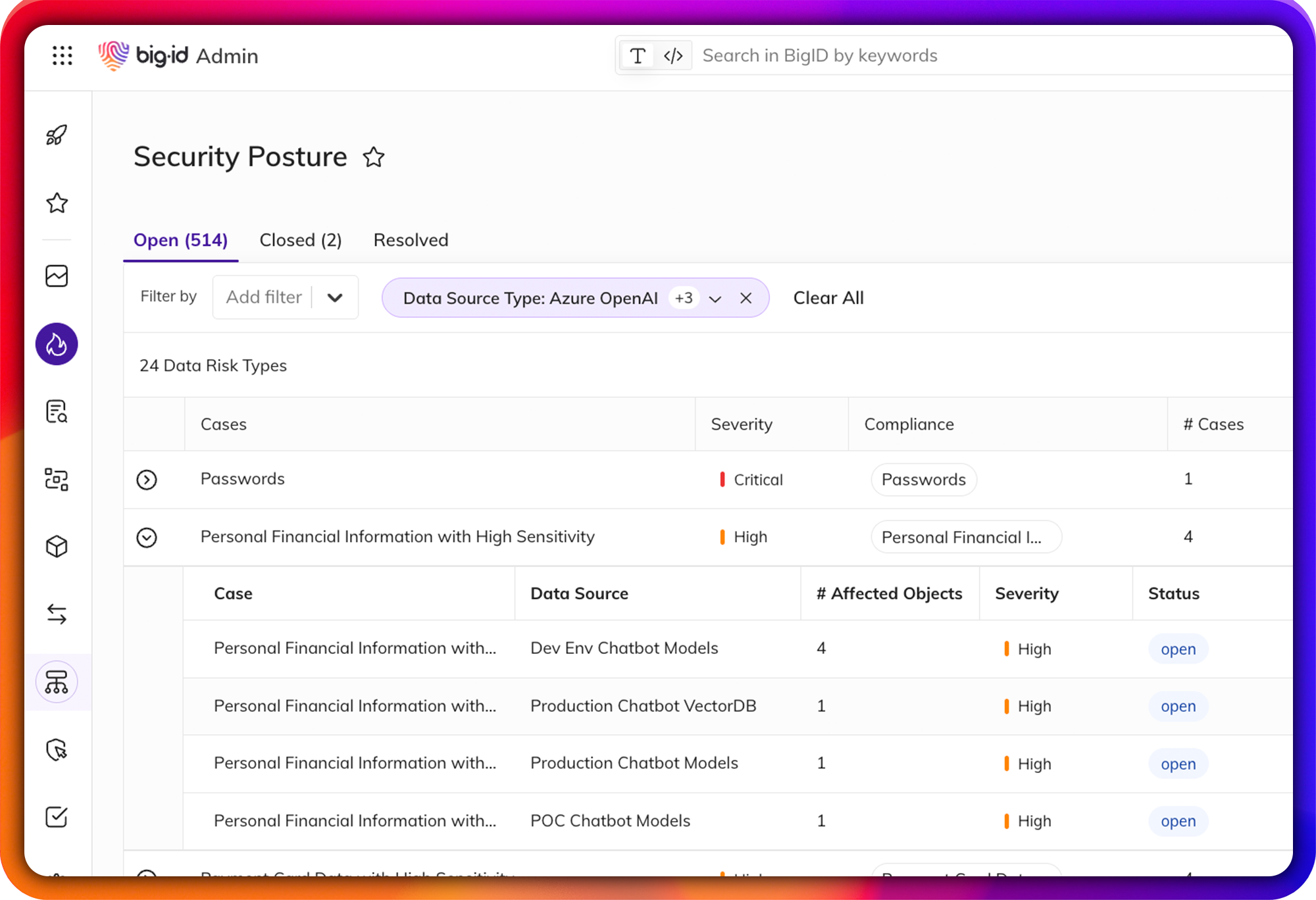
Improve ICT and Security Risk Management for DORA
Quickly assess and report on your data risk and vulnerabilities
DORA encourages financial institutions to implement robust cybersecurity measures, conduct regular risk assessments, and establish contingency plans to mitigate potential disruptions.
BigID enables organizations to identify and classify all of their sensitive data, allowing them to understand where their vulnerabilities exist, assess data risk, protect against unauthorized access, and quickly provide reporting to internal and external stakeholders.
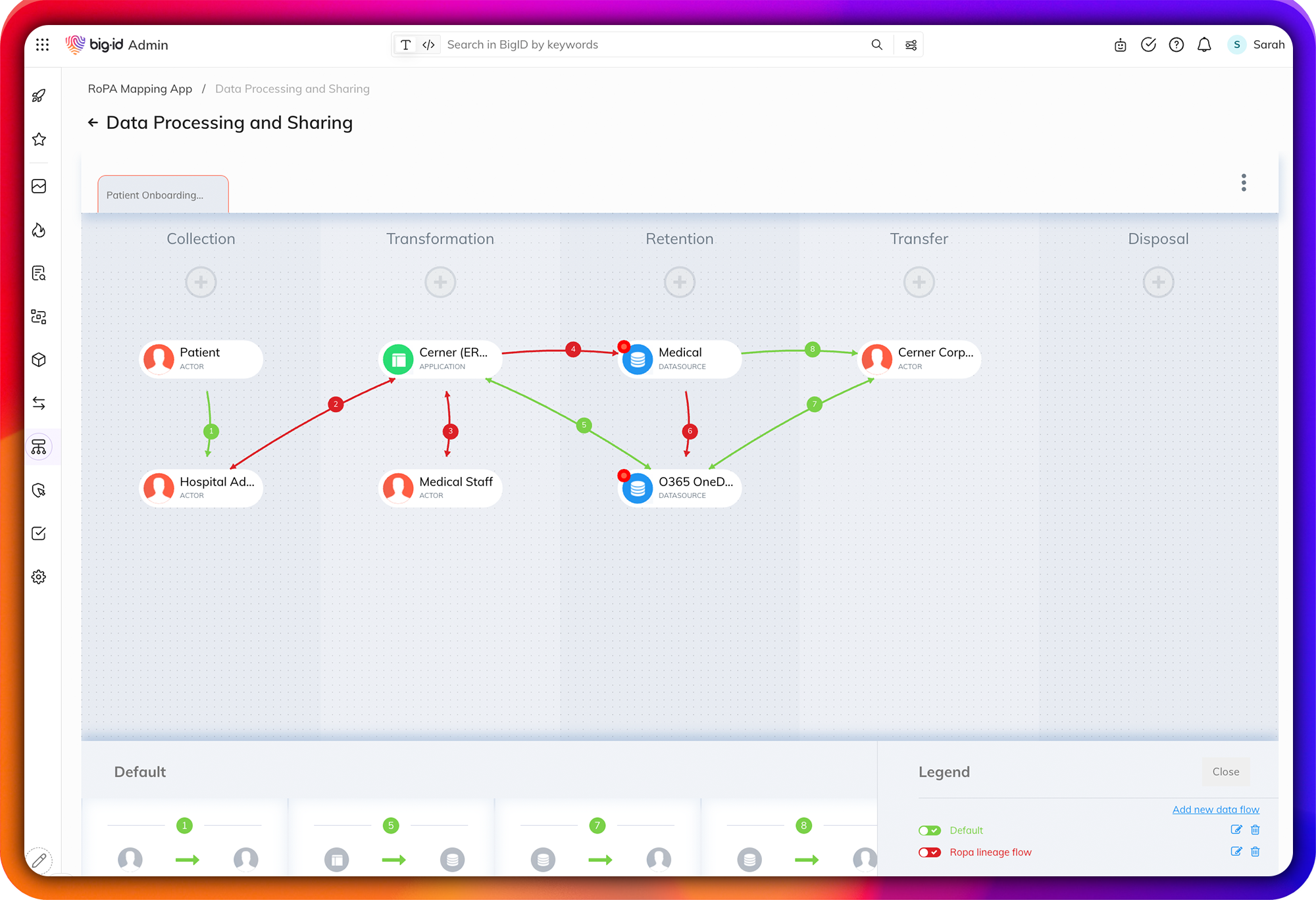
Map & Build a Complete Data Inventory for DORA
Gain complete visibility to understand how data is processed, transmitted, and stored
Identify and document data inventory to visually map data across the organization to assess how data is processed, transferred, and shared to reduce risk.
Discover all personal and sensitive information by identity, map the data relationships across sources, and visualize how data flows across your organization. Maintain an up-to-date and current documentation of how your data flows to comply with the DORA framework.
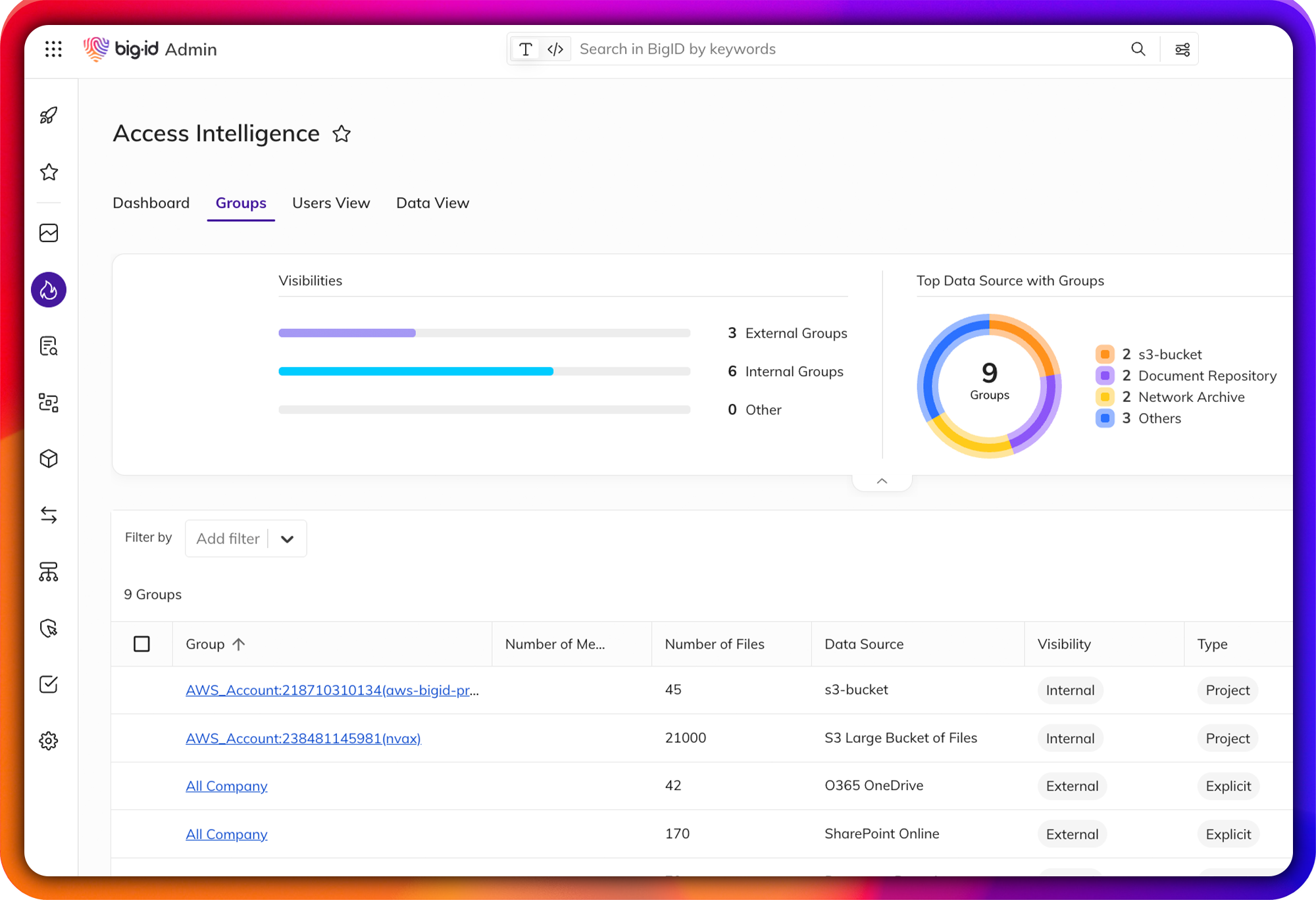
Enable Zero Trust for Data
Identify & remediate high-risk data access issues.
Easily find over-permissioned and over-exposed data across your entire data landscape: mitigate unauthorized use, reduce the risk of data leaks or breaches, get to a least privileged permissions model for zero trust, and enable compliance with DORA.
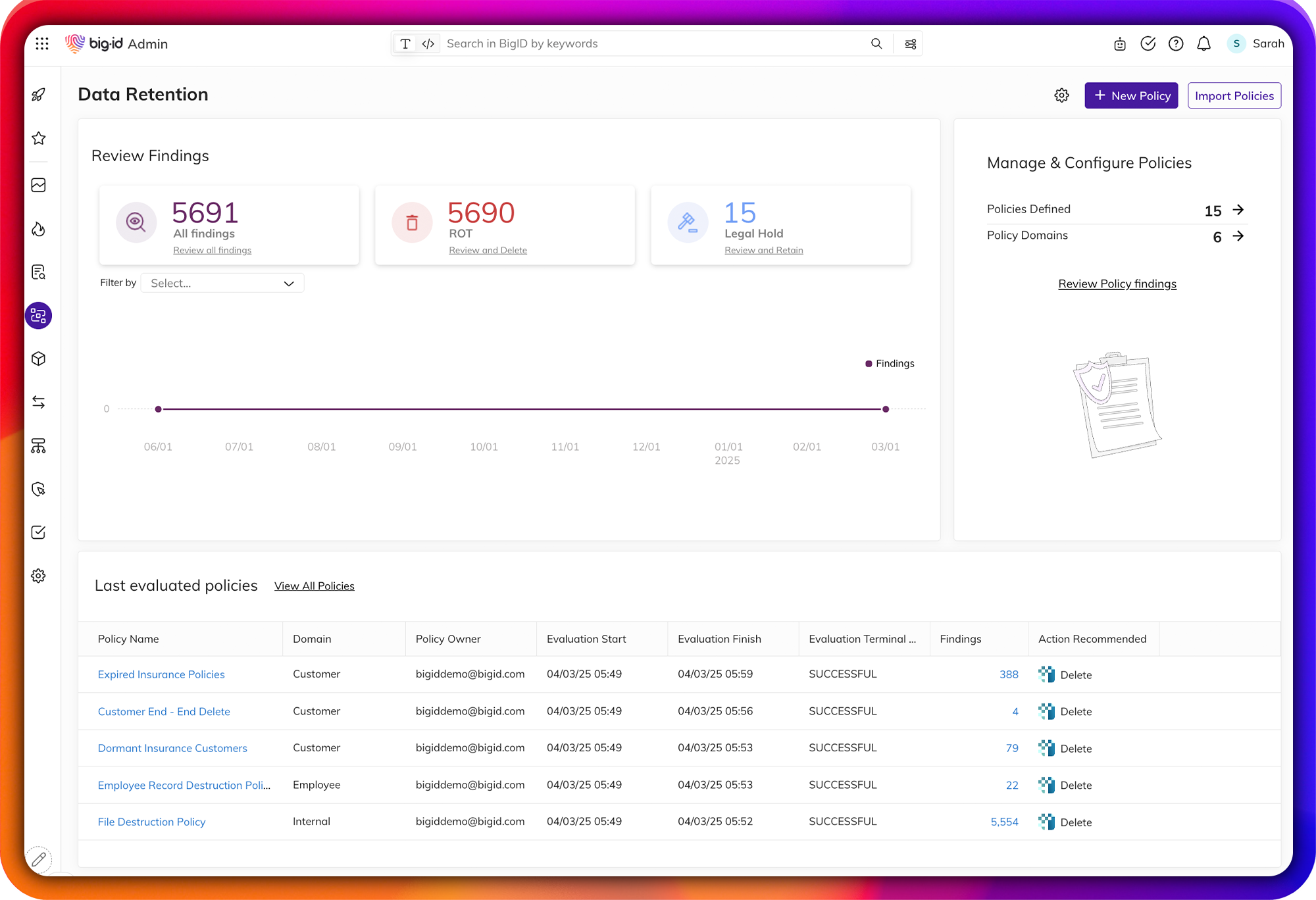
Automate Data Governance & Data Retention
Achieve end-to-end data lifecycle management at scale for DORA
Enforce policies around sensitive data and kick off remediation workflows with the Data Remediation App. Use the RoPA Data Mapping App to map sensitive and regulated data processing and sharing to assess the risk profile for a business process. Use the Data Retention App to detect data retention violations and carry out remediation wherever sensitive data exists. Identify and clean up duplicate and ROT data to minimize attack surfaces.
Simplify Breach Incident Response for DORA
Determine breach impact & streamline incident response and reporting
Assess the scope of a breach, identify impacted users and determine appropriate response plans. Determine whose data and attributes are impacted by a breach and systems and applications that have accessed the breached data source.
Comply with DORA breach reporting requirements to minimize financial, legal, and brand impact through automated workflows to facilitate response and notification.

Guide to Digital Operational Resilience Act (DORA) Compliance with BigID
Get everything you need to know to comply with the Digital Operational Resiliency Act (DORA) before the enforcement deadline on January 17th, 2025.
Download our comprehensive checklist to learn how your organization can achieve compliance with DORA while improving ICT risk management and building resilience against cyber threats.
