Strengthen your zero trust strategy with a data-first approach
Accelerate your zero-trust strategy: understand what data you have, reduce AI and user access based on sensitivity and data context, and get to a least privileged access model. Minimize risk in your data environment and remediate overprivileged users and AI models, overexposed data, and duplicate, unused data.
Talk to one of our data-centric zero trust specialists today 👇
-1.png)
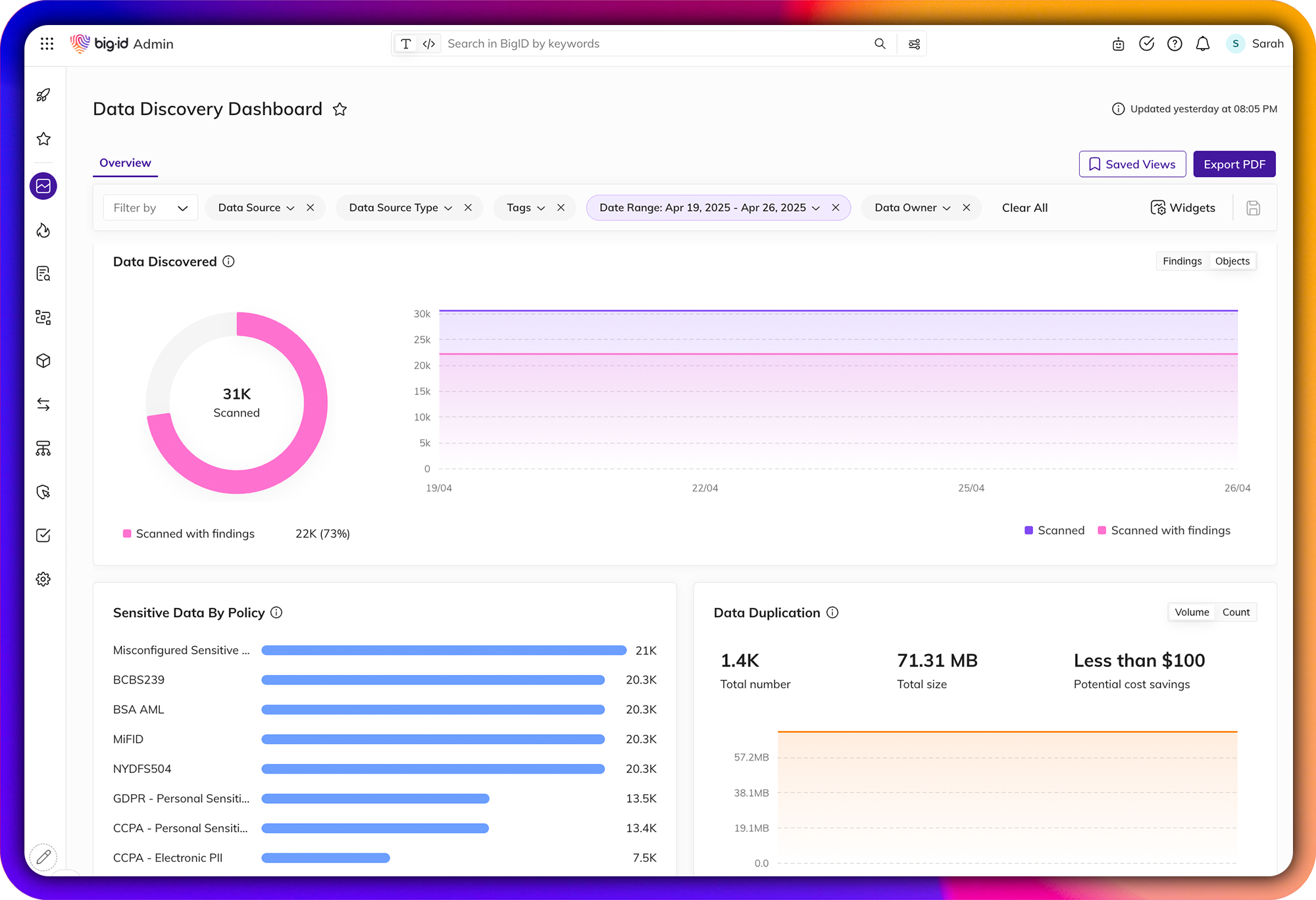
Shine a Light on Dark Data
Automatically find and inventory your most sensitive, critical, and high-priority data - wherever it lives.
Get unmatched data discovery and classification to find and protect the data that matters most to you: whether it's critical, regulated, personal, secrets, passwords, IP, financial, or more across structured and unstructured data. Get more accurate results every time with ML-driven data classification - across your entire data landscape (from on-prem to cloud to everywhere in between).
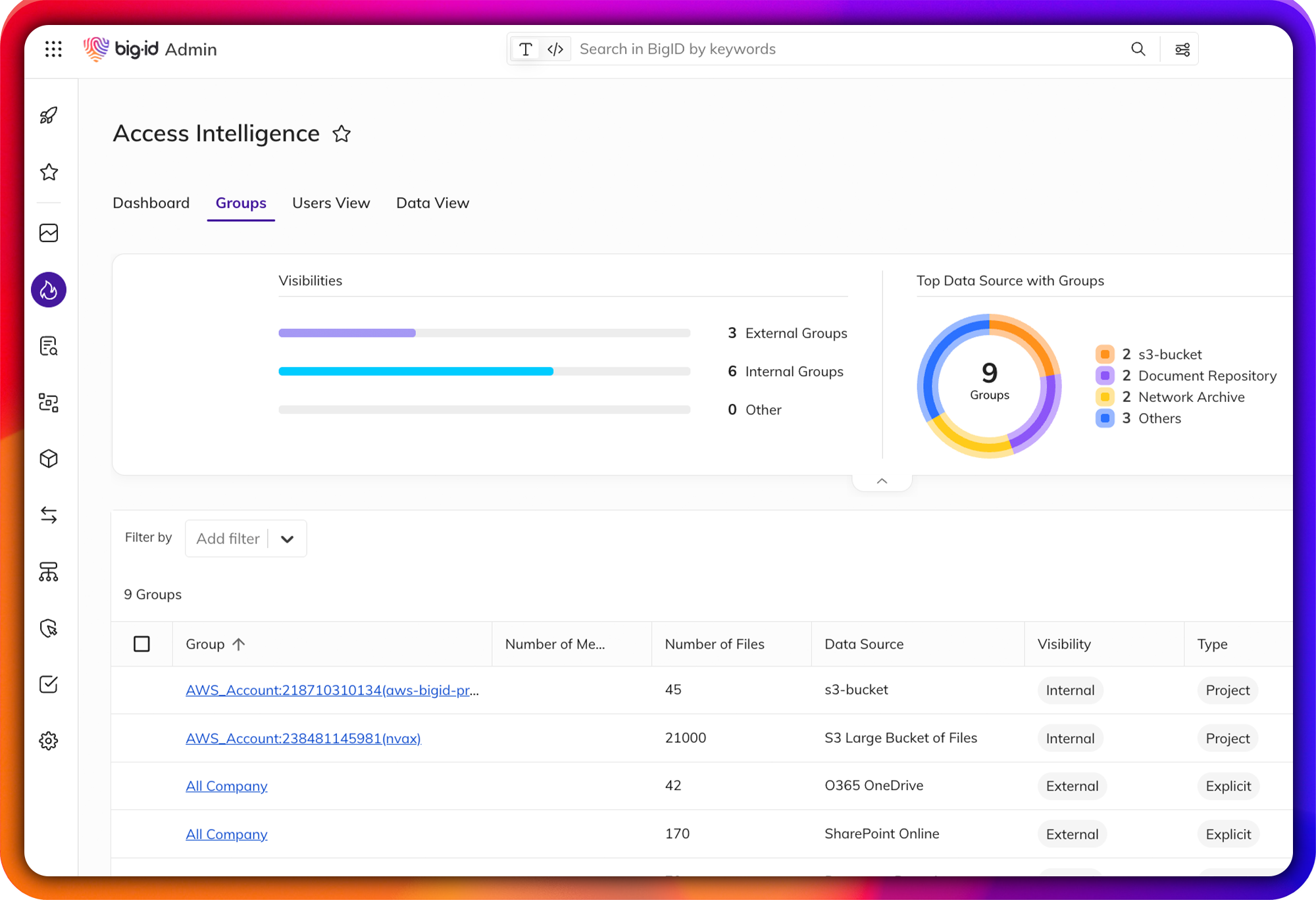
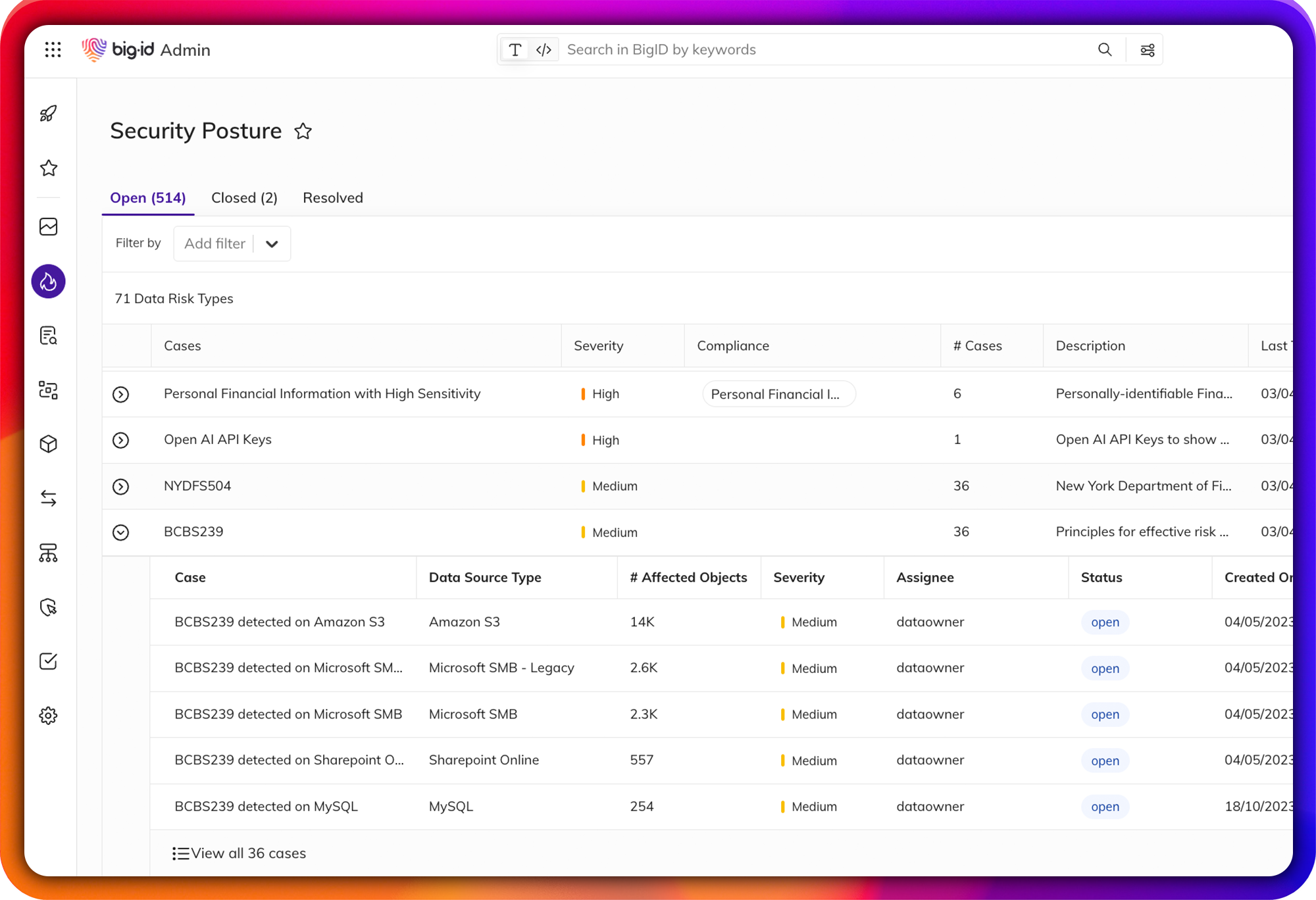
Enable Zero Trust for Data
Identify & remediate high-risk data access issues.
Easily find over-permissioned and over-exposed data across your entire data landscape: mitigate unauthorized use, reduce the risk of data leaks or breaches., and get to a least privileged permissions model for zero trust.
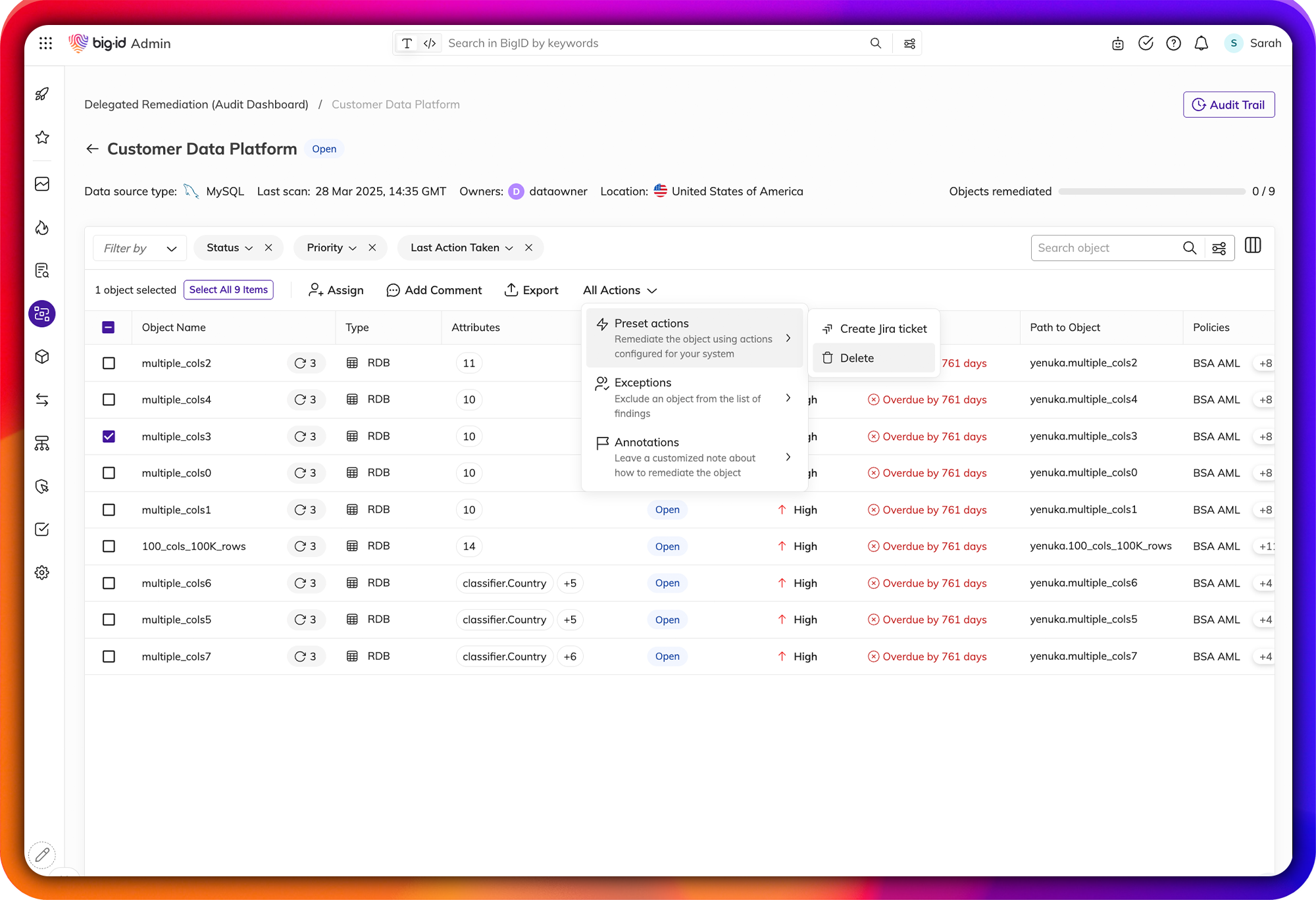
Streamline Data Protection Workflows
Remediate high-risk, sensitive, & critical data, everywhere.
Make it easier than ever for the right people to take the right actions, on the right data. Manage data protection all in one place - a single pane of glass to annotate, delete, quarantine, archive, mask, encrypt, and anonymize sensitive data.
Assign findings and tasks to the right data owners, take action on the right data, and maintain an audit trail of all data protection activity. Enforce and prioritize your remediation actions by policy and report on actions taken on sensitive data.
Data-Centric, Risk-Aware Security for the Multi-Cloud & Beyond
Get ahead of AI security challenges with a data-first approach.BigID helps you proactively identify sensitive, toxic, and high-risk data fueling AI models, so you can reduce exposure, ensure compliance, and minimize risk. Whether it's PII, IP, or shadow AI, BigID gives security teams the visibility and control they need across multi-cloud and on-prem environments, from training data to AI pipelines.
DSPM Spotlight: Access Intelligence
Take a quick interactive tour to see how BigID can help your organization minimize data access risk and enable zero trust.

DSPM Spotlight: Access Intelligence
Take a quick interactive tour to see how BigID can help your organization minimize data access risk and enable zero trust.